The Agentic Flattening
Twitter caused a real problem for the world. They “flattened” different contributors (experts, amateurs, trolls) into one feed with the same visual weight. You lost the contextual cues (credentials,
Search for a command to run...
Twitter caused a real problem for the world. They “flattened” different contributors (experts, amateurs, trolls) into one feed with the same visual weight. You lost the contextual cues (credentials,
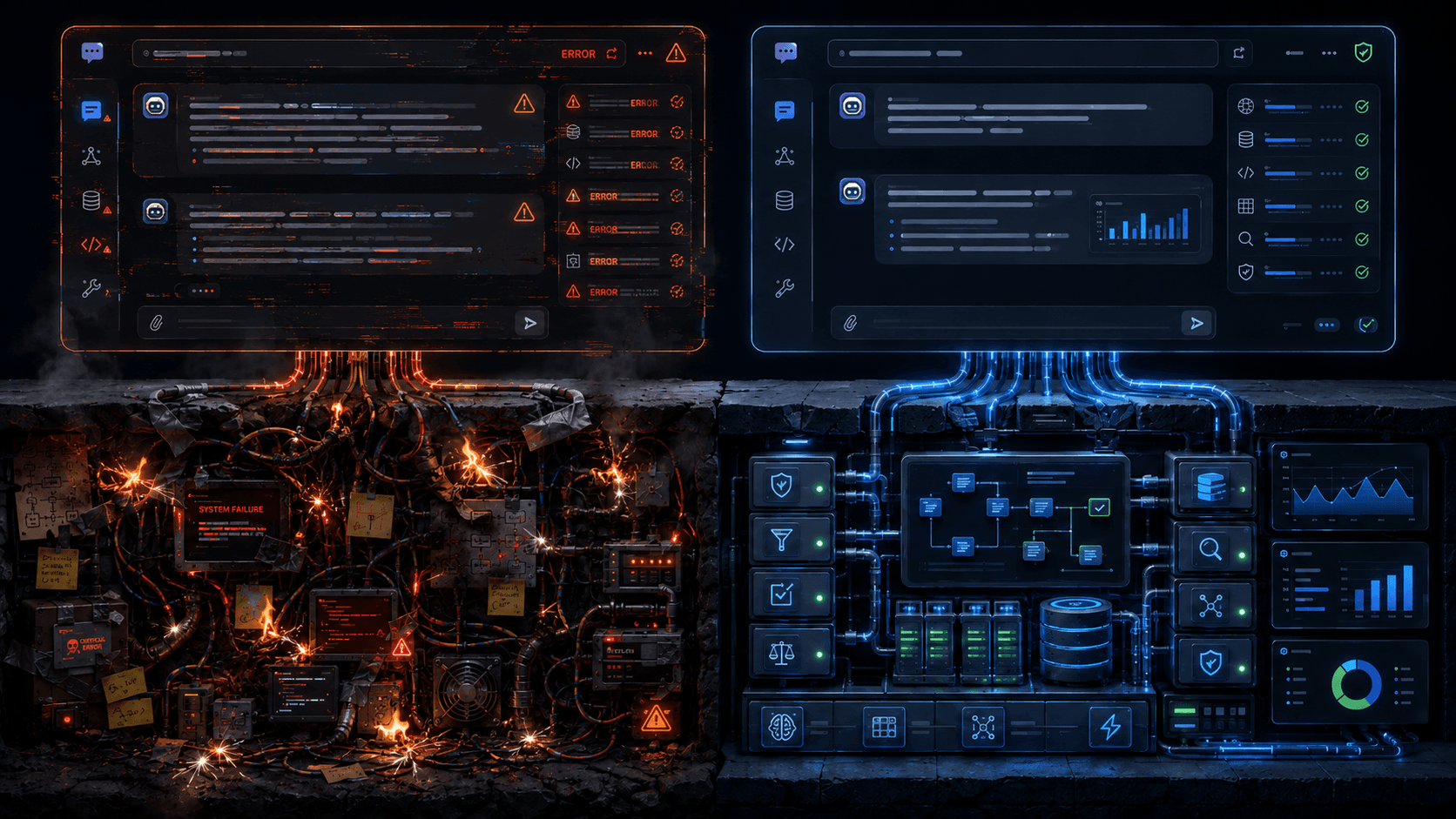
An AI-native approach to a broken system
The React2Shell bug is giving me major déjà vu, and I think there are important lessons here in Abstract vs. Concrete Risk (maybe in B2B sales too—I haven’t fully thought that part through yet). In the 2010s, the Apache Struts team made (what appears...
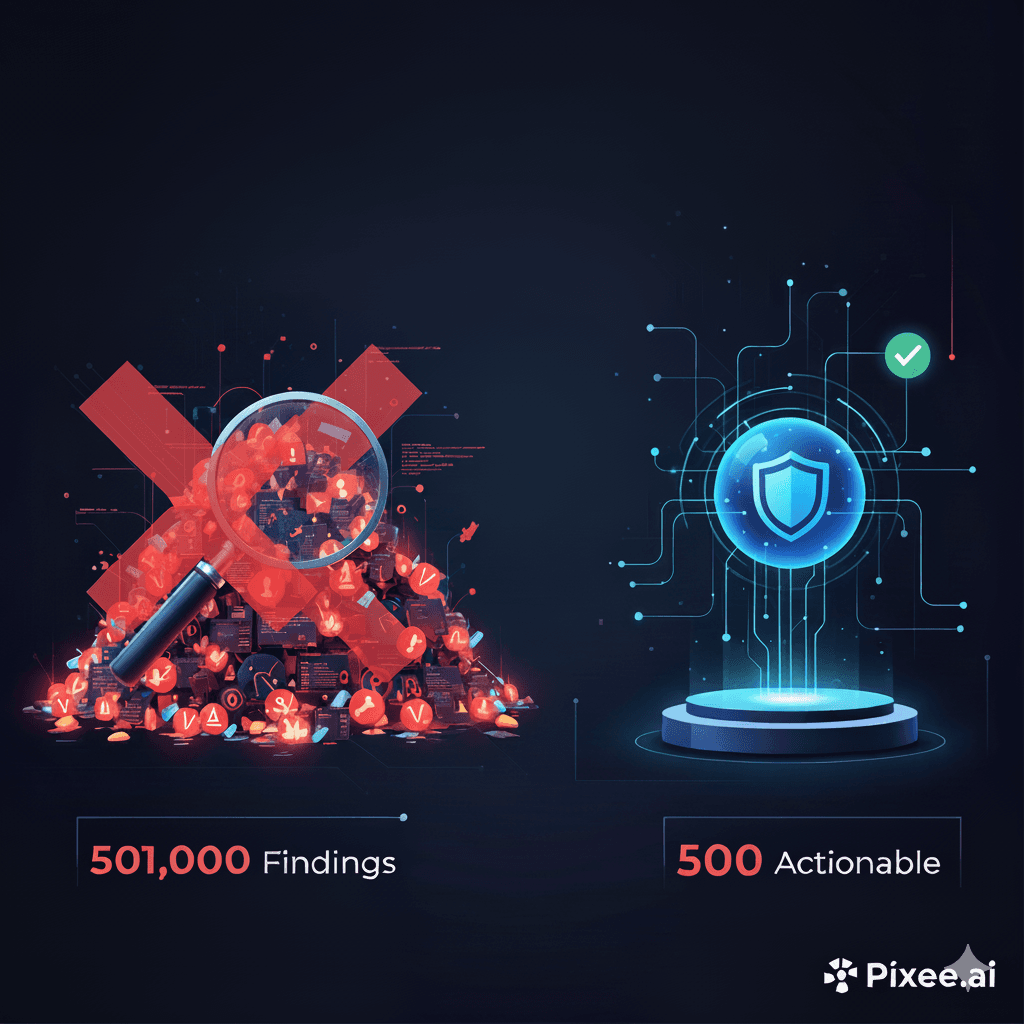
To do vulnerability triage, we use a number of tools: composable agents, workflows, zero-shot LLM calls, deep research, knowledge bases, code analysis tools — you get it. But, does any of it matter? We need to know if a simple “AI wrapper” from some ...
Research proves AI can fix code in OSS. Enterprise rollouts demand tenant context, governance, and proof.

The Counterintuitive Choice Breaking Today’s Security Programs Every CISO faces a moment of truth during application security tool evaluation and selection — a decision that will determine the success to vulnerability management at scale. Two vendors...
An interview with Staff Product Designer Terra Caussin on bridging the gap between security and usability

The Industry Needs Remediation, Not Just Prioritization
At Pixee, we need open source to do what we do, and we’re not alone. Research out of Harvard Business School by Manuel Hoffmann, Frank Nagle, and Yanuo Zhou estimates the demand-side value of open source to be $8.8 trillion (yes, TRILLION!). As we le...